The error message “ssh: connect to host <host> port 22: Connection refused” typically indicates that your SSH client is unable to establish a connection with the SSH server.
It can occur due to various reasons. The SSH server may not be running on the remote host, the host or IP address provided could be incorrect, the SSH server may be using a different port than the default port 22, a firewall might be blocking the SSH connection, or there could be network connectivity issues between the client and server.
In this article, we will dive into this issue.
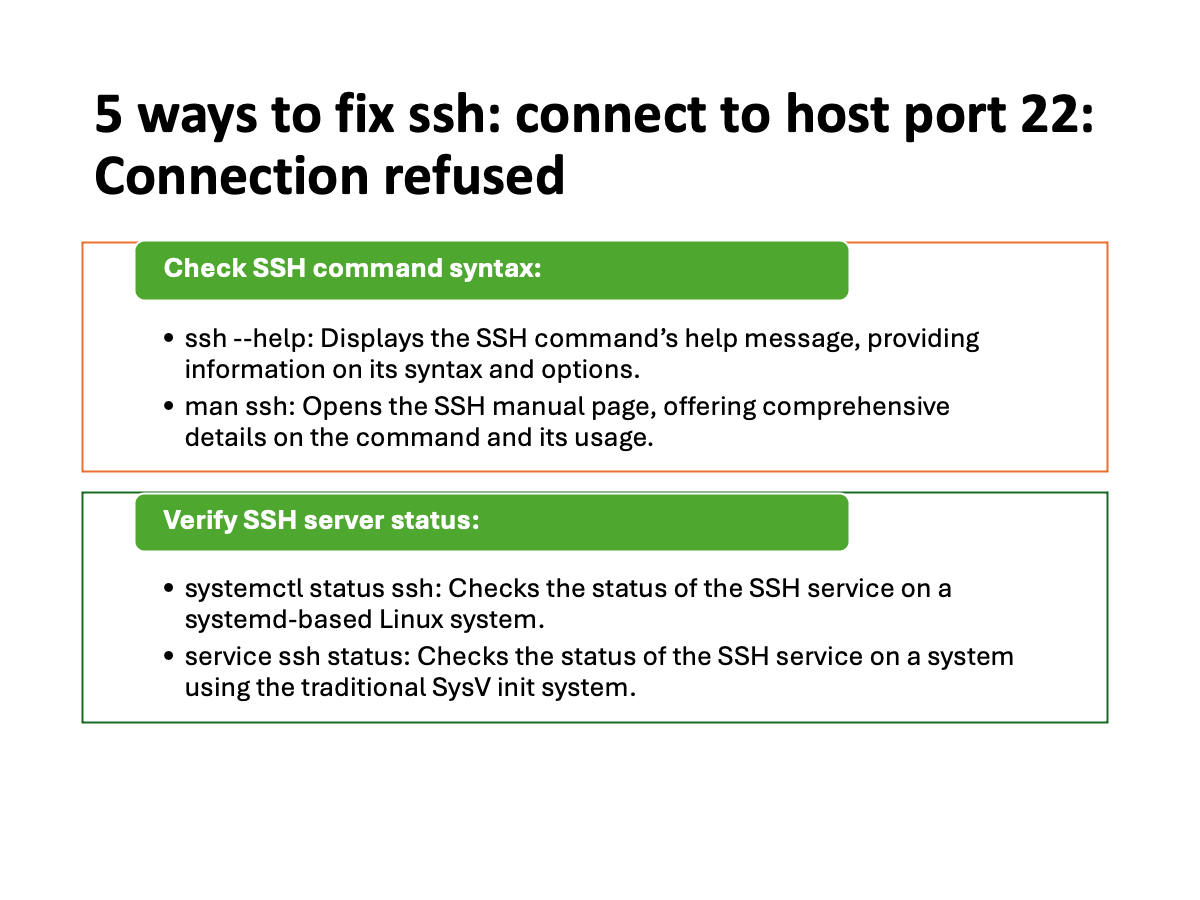
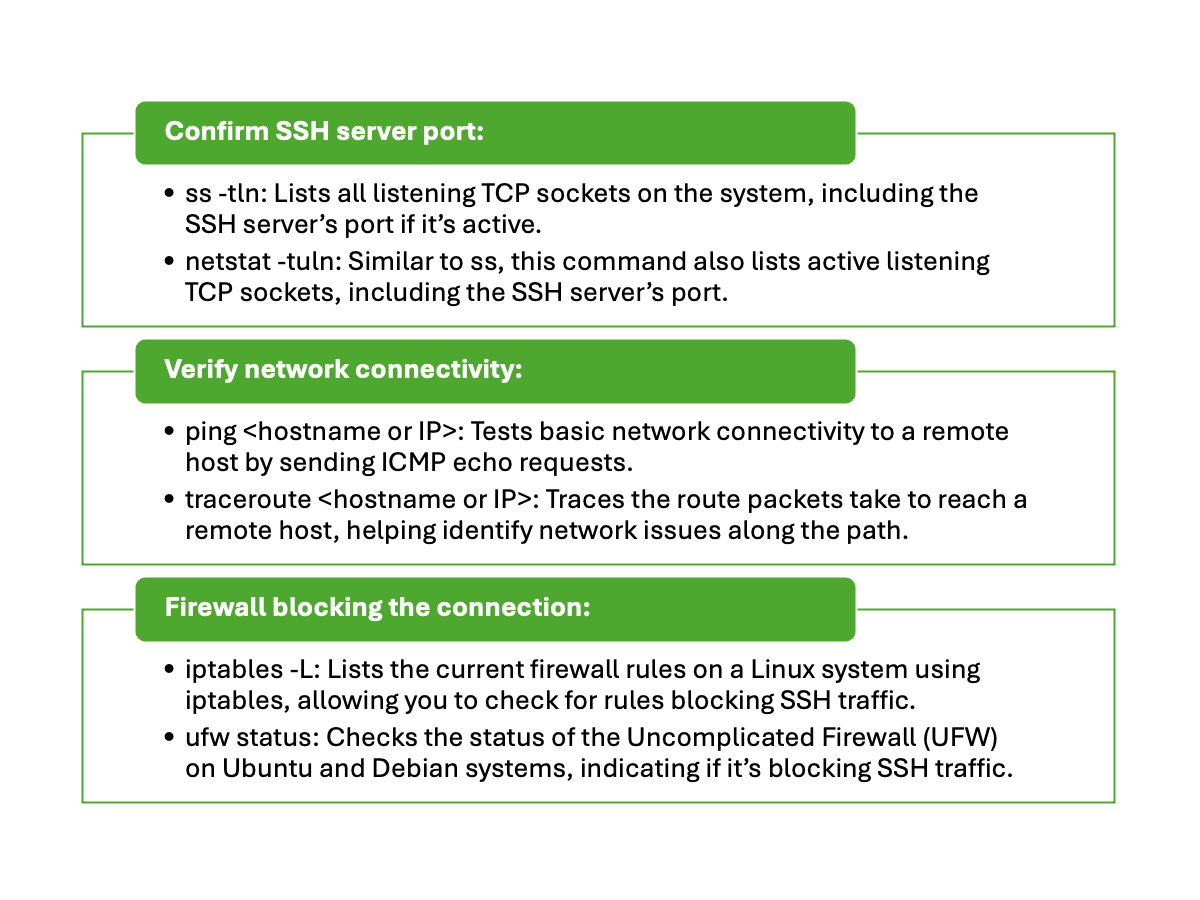
Table of Contents
Check SSH command syntax
The syntax for the SSH command is as follows:
ssh [options] [user@]hostname [command]
Here is a brief explanation of each part of the syntax:
- ssh – This is the command to initiate the SSH connection.
- [options] – This is an optional parameter that allows you to specify additional options to configure the SSH connection. For example, you can use the -p option to specify a non-standard SSH port.
- [user@]hostname – This is the remote host that you want to connect to. You can optionally specify a username to use for the SSH connection. If you omit the username, the default username for your current session will be used.
- [command] – This is an optional parameter that allows you to specify a command to run on the remote host after the SSH connection is established. If you omit this parameter, you will be dropped into an interactive shell on the remote host.
Here is an example of how to use the SSH command to connect to a remote host:
See also: Mastering the Linux Command Line — Your Complete Free Training Guide
This will initiate an SSH connection to the host example.com using the username username.
If you have already set up SSH keys, you will be logged in without being prompted for a password. If not, you will be prompted to enter your password.
Verify SSH server status
Ensure that the SSH server is running and accessible on the host you are trying to connect to.
Log in to the host using an alternative method like remote desktop or console access, and check the SSH server’s status with the following systemctl command:
systemctl status sshd
sudo systemctl status sshd.service
ssh.service - OpenBSD Secure Shell server
Loaded: loaded (/lib/systemd/system/ssh.service; enabled; vendor preset: enabled)
Active: active (running) since Thu 2022-06-23 17:44:36 UTC; 1 day 3h ago
Docs: man:sshd(8)
man:sshd_config(5)
Main PID: 829 (sshd)
Tasks: 1 (limit: 9535)
Memory: 5.1M
CGroup: /system.slice/ssh.service
└─829 sshd: /usr/sbin/sshd -D [listener] 0 of 10-100 startups
Jun 23 17:44:35 ubu2004 systemd[1]: Starting OpenBSD Secure Shell server...
Jun 23 17:44:36 ubu2004 sshd[829]: Server listening on 0.0.0.0 port 22.
Jun 23 17:44:36 ubu2004 sshd[829]: Server listening on :: port 22.
If the SSH server is not running, start it using the appropriate command for your system. For example:
systemctl start sshd
Confirm SSH server port
By default, SSH servers listen on port 22. However, it’s possible that the SSH server on the host you’re trying to connect to is configured to use a different port.
To check which port the SSH server is using, you can follow these steps:
Log in to the server where the SSH server is running. You can use an alternative method like remote desktop or console access if you cannot establish an SSH connection.
Once you’re logged in to the server, open a terminal or command prompt.
Run the following command to view the SSH server’s configuration file:
sudo nano /etc/ssh/sshd_config
This command opens the SSH server configuration file in the Nano text editor. Look for the line that specifies the port number. It typically looks like this:
Port 22
If the port number is set to the default value of 22, it means the SSH server is using the default port. If a different port number is specified, take note of that number.
After noting the port number, press Ctrl+X to exit the Nano editor. You will be prompted to save the changes made to the file. If you did not make any changes, simply press N to exit without saving.
Remember, if the SSH server is using a non-standard port, you will need to specify that port when connecting to the server using SSH. For example:
ssh -p port_number username@host
If you do not have access to the server’s configuration file, you can also try checking the SSH server’s status and listening ports by running the following command:
sudo netstat -tlnp | grep ssh
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 4012596/sshd
tcp6 0 0 :::22 :::* LISTEN 4012596/sshd
Here -tlnp is the shortened form of the –listen –tcp –process –numeric arguments.
This command will display the active TCP connections and listening ports on the server. Look for the line that includes “ssh” to find the port number being used by the SSH server.
Verify network connectivity
Verifying network connectivity is an important step when troubleshooting the “ssh: connect to host <host> port 22: Connection refused” error.
It helps determine if there are any network-related issues that might be preventing your SSH client from reaching the SSH server.
The ping command is a common tool used to test network connectivity between two devices. When you execute the ping <host> command, your computer sends a small network packet to the specified host, and if the host is reachable and responsive, it sends a reply back.
If the ping command returns a response from the host like below, it indicates that the network connection is working fine.
# ping google.com
PING google.com (142.250.189.174) 56(84) bytes of data.
64 bytes from sfo03s24-in-f14.1e100.net (142.250.189.174): icmp_seq=1 ttl=116 time=1.97 ms
64 bytes from sfo03s24-in-f14.1e100.net (142.250.189.174): icmp_seq=2 ttl=116 time=1.79 ms
64 bytes from sfo03s24-in-f14.1e100.net (142.250.189.174): icmp_seq=3 ttl=116 time=1.93 ms
In this case, the “ssh: connect to host <host> port 22: Connection refused” error is likely due to a different issue, such as the SSH server not running or a firewall blocking the SSH connection.
However, if the ping command fails to receive a response or shows that the host is unreachable, it suggests a network connectivity problem.
# ping howtouselinux.com
PING howtouselinux.com (164.92.86.53) 56(84) bytes of data.
^C
--- howtouselinux.com ping statistics ---
7 packets transmitted, 0 received, 100% packet loss, time 6150ms
Firewall blocking the connection
When encountering the “ssh: connect to host <host> port 22: Connection refused” error, one possible cause is a firewall blocking the SSH connection.
Firewalls are security measures that monitor and control network traffic, and they can be set up at different points within a network, including the SSH server or any intermediate network devices.
Firewalls often enforce rules that determine which network connections are allowed or blocked.
Determine if the firewall is on the SSH server itself or if it is located on an intermediate network device, such as a router or a dedicated firewall appliance.
If the firewall is located on an intermediate network device, such as a router, you need to configure it to permit SSH traffic to reach the SSH server.
There are a few different ways to check the status of the firewall on a Linux machine:
ufw (Uncomplicated Firewall) is a user-friendly firewall that is installed by default on many Linux distributions. To check the status of ufw, use the status command:
sudo ufw status
This will show you whether ufw is active or inactive, as well as the rules that are currently in place.
If ufw is not installed on your machine, you can use the iptables command to check the firewall rules. To see the current firewall rules, use the -L flag:
sudo iptables -L
This will show you the rules that are currently in place for the different chains (INPUT, FORWARD, and OUTPUT).
Alternatively, you can use the firewall-cmd command, which is part of the firewalld service. To check the status of the firewall, use the –state flag:
sudo firewall-cmd --state
This will show you whether the firewall is running or not. To see the current firewall rules, use the –list-all flag:
sudo firewall-cmd --list-all
This will show you the rules that are currently in place for the different zones.
Hence, ensure you have the SSH port allowed in your firewall. If you are using UFW, you can run the command:
sudo ufw allow 22/tcp
sudo ufw reload
This should add port 22 to the firewall settings and allow incoming and outgoing connections. If SSH is running on a different port, replace the port 22 with your target port.
If you are using firewall-cmd on Fedora or REHL family, you can run the command:
sudo firewall-cmd --permanent --add-port=22/tcp
sudo firewall-cmd --reload
Similarly, replace the port 22 with the port of your SSH server.
If you are using iptables, you can run the command:
sudo iptables -A INPUT -p tcp --dport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT
sudo iptables -A OUTPUT -p tcp --sport 22 -m conntrack --ctstate ESTABLISHED -j ACCEPT
As a troubleshooting step, you can temporarily disable the firewall(s) to determine if they are indeed the cause of the connection issue. This should only be done for testing purposes and should not be a permanent solution. Always exercise caution when making changes to firewall configurations.
After implementing these steps, try connecting to the remote host again using the SSH command.
If the issue persists, carefully review the error message to identify any specific details that might help pinpoint the problem.
Additionally, check the SSH server’s logs (/var/log/auth.log on Ubuntu/Debian or /var/log/secure on CentOS/RHEL) for more information on the connection issue.


I login the sever with console and found that my sshd service was inactive dead. I restarted it and everything became good.
Thanks for the detailed guide.
Excellent info.
I found the tip about checking the server name and IP address to be very useful. A simple typo can sometimes lead to this error.
It would be great if the article also included a brief explanation of SSH host keys and how they play a role in secure connections.